|
|
|
|
Next area is
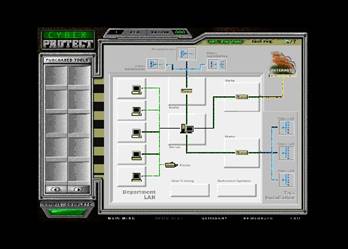
Canned Attack Defend
|
|
Characteristics
|
|
Canned rules,
|
|
Limited (but
often numerous) scenarios, fixed decision tree execution paths
|
|
Often some
random elements
|
|
High up front
building costs – multimedia package like Visual Basic, Macromedia Authorware:
Rule of thumb (conservative) – 300 man hours for each hour of output
|
|
|
|
“I liked cyber
protect because”:
|
|
- It felt real,
programs got stale and needed updating. It exploited where I was weak
|
|
- Overall, this
is an excellent product and one which I will take home to my network
professionals and insist they give me a certificate.
|
|
- I found the
CyberProtect exercise to be very instructional. It did take me a while to get through the
exercise but I was finally successful.
It was a good exercise and very informative.
|
|
- I found
CyberProtect to be an excellent tool to test the knowledge of someone charged
to protect an agency's infrastructure.
This is a tool that I will take back and provide to my team, and
others within the department.
|
|
- When using the
tool, one would quickly found out that if you did not at least cover your
bases you were exposed and open to attacks.
This did not mean you had to purchase the high-end tools, but
strategically placing low end items were the network could handle it, and
balancing between the middle to high ranges.
Upgrades could be applied if funds were available later on.
|
|
- Overall,
hands-on allows the students to understand the process. There were issues that were raised that
provoked questions.....the whole purpose of the exercise.”
|
|
|